本集简介
双语字幕
仅展示文本字幕,不包含中文音频;想边听边看,请使用 Bayt 播客 App。
今天是2015年12月15日,星期二,一名嫌疑人已在VTech儿童玩具黑客事件中被捕。
It's Tuesday, 12/15/2015, and a suspect has been arrested in the VTech kids toy hacking case.
英国警方几小时前逮捕了一名21岁的男子,这是对此次黑客事件持续调查的一部分。
UK police slapped the cuffs on a 21 year old man just a few hours ago as part of an ongoing investigation into the hacking.
据估计,近六百五十万个儿童档案和近五百万人的成人账户在此次黑客事件中遭到泄露,这可能是近年来最无耻的黑客事件之一。
Estimates indicate almost six and a half million kids profiles and almost 5,000,000 adult accounts were compromised in what might be described as the most unscrupulous hack to hit headlines in years.
虽然没有获取到信用卡信息,但儿童的姓名和地址 reportedly被访问,这不仅让VTech颜面尽失,更令人毛骨悚然。
No credit card info was obtained, but children's names and addresses are said to have been accessed, which aside from being a black eye on VTech, is just straight up creepy.
嫌疑人尚未公布姓名,但直觉告诉我,他接下来在狱中的日子恐怕不会好过。
The suspect hasn't yet been named, but something tells us his next few days behind bars probably won't be so enjoyable.
节日快乐,变态。
Happy holidays, creep.
这是《暗网日记》,来自互联网黑暗面的真实故事。
This is Darknet Diaries, True stories from the dark side of the Internet.
我是杰克·雷西德。
I'm Jack Recider.
本集由DeleteMe赞助。
This episode is sponsored by DeleteMe.
DeleteMe让移除您的在线个人信息变得简单、快捷且安全,尤其是在监控和数据泄露日益普遍、人人皆可能受害的今天。
DeleteMe makes it easy, quick, and safe to remove your personal data online at a time when surveillance and data breaches are common enough to make everyone vulnerable.
如今,要在网上找到关于个人的隐私信息比以往任何时候都容易。您的地址、电话号码和家人姓名暴露在网络上,可能会在现实世界中带来实际后果,使每个人面临风险。
It's easier than ever to find personal information about people online, Having your address, phone number, and family members' names hanging out there on the Internet can have actual consequences in the real world and makes everyone vulnerable.
隐私对我来说是一个极其重要的议题。
Privacy is a super important topic to me.
因此,几年前我注册了DeleteMe服务,它立即开始在网上搜索我的信息,并向我提供发现结果的报告。
So a few years ago, I signed up, and DeleteMe immediately got busy scouring the Internet, looking for my name, and then gave me reports on what they found.
然后,它开始删除这些信息,并向我展示它移除了哪些内容。
And then they got busy deleting things, showing me what they got rid of.
在隐私保护方面,有人为我保驾护航真是太好了。
It's great to have someone on my team when it comes to my privacy.
立即注册DeleteMe,掌握您的数据,保护您的私人生活不被泄露。
Take control of your data and keep your private life private by signing up for DeleteMe.
现在,作为给我的听众的特别优惠,访问 deleteme.com/darknetdiaries 并在结账时使用促销码 d d 20,即可享受 DeleteMe 计划 20% 的折扣。
Now at a special discount for my listeners, you can get 20% off your DeleteMe plan when you go to join deleteme.com/darknetdiaries, and use promo code d d 20 at checkout.
获得 20% 折扣的唯一方法是访问 join deleteme.com/darknetdiaries,并在结账时输入代码 d d 20。
The only way to get 20% off is to go to join deleteme.com/darknetdiaries and enter code d d 20 at checkout.
就是 join deleteme.com/darknetdiaries,代码 d d 20。
That's join deleteme.com/darknetdiaries code d d 20.
本集由 Zocdoc 赞助。
This episode is sponsored by Zocdoc.
找到一位你真正喜欢的医生,就像在沙子里淘出钻石一样。
Finding a doctor you actually like feels like discovering a diamond in the rough.
当然。
Sure.
你希望找一个在保险网络内、离得近、有空档时间的医生,但说实话。
You want someone that's in network, nearby, with open time slots, but let's be honest.
这还只是开始。
That's just the start.
能找到一个真正认真倾听、解释清楚的人,那就更好了。
It'd also be nice to find someone who really listens and explains things clearly.
你理想中的那一位医生是存在的,而在ZocDoc上找到他们非常容易。
Your diamond in the rough doctor exists, and finding them is easy on ZocDoc.
ZocDoc是一个免费的应用程序和网站,帮助你寻找并预约高质量的网络内医生,让你找到心仪的人选。
ZocDoc is a free app and website that helps you find and book high quality in network doctors so you can find someone you love.
我们覆盖了全美50个州的15万多名医疗提供者。
We're talking more than a 150,000 providers across all 50 states.
你想亲自去看医生吗?
Wanna see your doctor in person?
很好。
Great.
你更喜欢视频问诊吗?
Do you prefer a video visit?
他们也可以提供视频问诊。
They can do that too.
通过ZocTalk预约的就诊通常在预订后24至72小时内就能安排。
And appointments made through ZocTalk happen fast, typically within twenty four to seventy two hours of booking.
你甚至可以约到当天的就诊。
You can even score same day appointments.
我很 impressed 于在需要时,搜索他们的网站并找到医疗提供者是如此快速和便捷。
I'm impressed with how quickly and easy it is to search their site and find health care providers when you need it.
所以别再拖延这些医生预约了,立即前往 zocdoc.com/darknet 找到并立即预约你喜爱的医生。
So stop putting off these doctor's appointments and go to zocdoc.com/darknet to find and instantly book a doctor you love today.
拼写是 z o c d o c。
That's spelled z o c d o c.
Zocdoc.com/darknet。
Zocdoc.com/darknet.
Zocdoc.com/darknet。
Zocdoc.com/darknet.
感谢Zoc doc对本节目的支持。
Thanks, Zoc doc, for supporting this show.
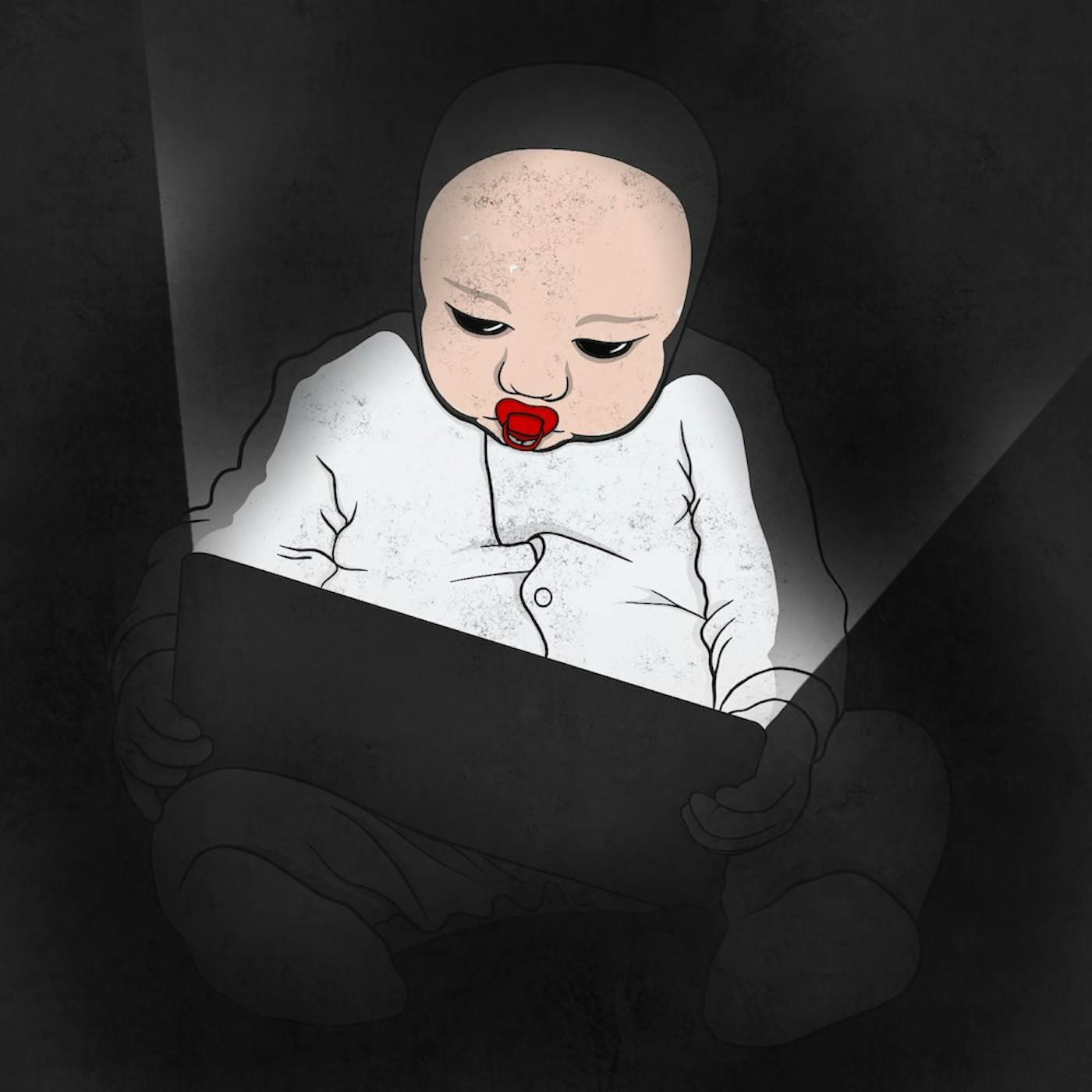
现在的孩子看到父母使用平板电脑和手机,也想玩一玩。
Kids today see their parents using tablets and phones, and they want to play too.
玩具制造商试图抓住这一机会,推出了儿童专用的平板电脑和智能手表。
Toymakers have tried to capitalize this by offering child friendly tablets and smartwatches.
这些儿童专用设备像其他平板电脑一样,可以联网并连接到互联网。
These kid friendly devices are online and connected to the Internet just like any other tablet.
它们具备让孩子通过平板向父母手机发送消息的功能。
They have features that let the child send messages from their tablet to their parent's phone.
不仅仅是聊天。
Not just chats, though.
孩子还可以发送图片、视频或语音录音。
The kid can send pictures, videos, or voice recordings.
VTech 是生产这类儿童专用设备的厂商之一。
VTech is one maker of these kind of kid friendly devices.
他们生产专为儿童设计的平板电脑和手机应用。
They make tablets and phone apps that are specifically designed for kids.
当你购买一台VTech平板时,它会要求你注册该设备。
When you buy a VTech tablet, it asks you to register the device.
他们要求提供父母的姓名、物理地址以及用户名和密码。
They ask for the parent's name and the physical address as well as the username and password.
然后,这款儿童平板还会询问孩子的姓名、性别以及生日。
Then the toy tablet also asks for the child's name, if they are a boy or a girl, and what their birthday is.
它甚至建议你拍摄一张孩子使用平板的照片来建立个人资料。
It even suggests you take a picture of the child using the tablet to set up a profile.
这种注册方式允许父母的手机连接到孩子的平板。
This registration allows a parent's phone to connect to their kid's tablets.
VTech开发的将父母手机与儿童平板连接的技术被称为KidConnect。
The technology VTech created that connects a parent's phone to a kid's tablet is called KidConnect.
VTech还创建了自己的应用商店,名为Learning Lodge,你可以在平板上下载应用程序、游戏和书籍。
VTech also created its own app store called the Learning Lodge, where you can use their tablet to download apps, games, and books.
猜猜看,当黑客获得这些儿童平板时会发生什么?
Take a guess at what happens when hackers get ahold of these toy tablets.
他们最终将平板电脑的性能推到了极限。
They end up pushing the tablets to the limits.
有一个专门针对破解VTech平板电脑的论坛。
There's a forum dedicated to hacking the VTech tablets.
人们已经能够做各种各样的事情。
People have been able to do all sorts of things.
一位黑客将设备拆开,用烙铁成功进入了底层操作系统,那是Linux。
One hacker took the thing apart and with a soldering iron was able to get into the underlying operating system, which is Linux.
从那里,黑客们获得了系统的根权限。
From there, the hackers were able to get root access to it.
后来,有人向我们展示,他们成功让这个小玩具平板运行了Doom——那款上世纪九十年代的旧PC游戏。
Then eventually, someone showed us they got the little toy tablet to play Doom, that old PC game from the nineties.
硬件黑客社区常说的是:如果你打不开它,你就不是真正的拥有者。
The hardware hacker community is often heard saying, if you can't open it, you don't own it.
就像合法地修理自己的汽车一样,修改你所拥有的电子产品也是合法的。
Just like it's legal to do work on your own car, it's also legal to modify the electronics you own.
你可能会使保修失效,但拆开它并随意改装并不违法。
You may void the warranty, but it's not illegal to take it apart and do whatever you want to it.
随着这个论坛的流行,它最终吸引了一种不同的黑客。
As this forum grew in popularity, it eventually attracted a different kind of hacker.
这位不是硬件黑客,而是一个网络黑客。
Instead of a hardware hacker, this guy was a network hacker.
他浏览了一下,发现这些平板电脑经常与一个名为planetvtech.com的网站通信。
He browsed around and found the tablets talk frequently to a website called planetvtech.com.
他查看了这个网站,几乎立刻发现它存在SQL注入漏洞。
He took a look at that website and almost immediately found it was vulnerable to SQL injection.
SQL注入是网站面临的首要风险。
SQL injections are the number one risk websites face.
它利用代码的薄弱环节,试图攻击底层数据库。
It takes advantage of weak code and tries to exploit the underlying database.
像这样的网络黑客通常已经配备了大量自动执行攻击的脚本和程序。
Network hackers like this are often already equipped with loads of scripts and programs that automatically execute an attack.
出于纯粹的好奇心,这名黑客仅用几下键盘操作,就运行了一个针对planetvtech.com的脚本,试图利用SQL漏洞。
Out of sheer curiosity, with a few keystrokes, this hacker ran a script against planetvtech.com, which attempted to exploit SQL.
令他惊讶的是,脚本成功了。
To his surprise, it worked.
他获得了该网站的shell访问权限。
He had shell access to the website.
又过了几下键盘操作,他就获得了root权限。
A few keystrokes later, he then had Root access.
他对自己说:‘天啊,见鬼了。’
He said to himself, quote, holy fuck.
我有了root权限。
I have root.
这太简单了。
That was easy.
我能找到什么?
What can I find?
引号结束。
End quote.
他完全掌握了planetvtech.com网站,拥有100%的控制权。
He had full access to the planetvtech.com website, 100% control of it.
一旦黑客进入网页服务器,他就开始四处查看。
Once the hacker was in the web server, he took a look around.
他看到了VTech网络中的许多其他服务器,包括一台数据库服务器。
He saw numerous other servers on the VTech network, including a database server.
他成功进入了数据库。
He was able to hop into the database.
当他查看时,发现数据库规模庞大。
And when looking around there, he found the database was huge.
黑客复制了数据库中的所有内容,下载了整个数据库,然后转向另一个数据库,也复制了那里的所有内容。
The hacker grabbed a copy of everything in the database, downloaded the whole thing, then moved on to another database and grabbed a copy of everything there too.
随后,黑客断开了与VTech服务器的连接。
The hacker then disconnected from the VTech servers.
他知道他犯了罪,一股紧张感席卷全身。
He knew he had committed a crime, and a wave of nervousness swept across him.
这次入侵发生在2015年11月16日左右。
This breach occurred around 11/16/2015.
这名黑客既感到失望,又感到兴奋。
The hacker was equal parts disappointed and excited.
他认为入侵网络实在太容易了。
He thought getting into the network was way too easy.
在很短的时间内,他就获取了他们多个数据库的全部内容。
In a very short time, he was able to take all the contents of their multiple databases.
有了VTech数据库的副本在自己的电脑上,他可以慢慢浏览,查看自己获得了哪些数据。
With a copy of the VTech database on his own computer, he was able to slowly go through it and see what data he had.
他首先注意到一个名为“parent”的数据表。
The first thing he noticed was a table called parent.
它包含以下字段:名字、姓氏、电子邮件地址、加密密码、密保问题、密保答案、家庭地址、IP地址。
It had the following fields, first name, last name, email address, encrypted password, secret question, secret answer, home address, IP address.
当黑客查看时,他意识到这是该网站所有注册用户的完整用户数据库。
As the hacker looked, he realized this is the entire user database for everyone who's registered at the site.
这个表中列出了480万人。
There were 4,800,000 people listed in this table.
他不敢相信自己的眼睛。
He could not believe his eyes.
一份包含480万个用户账户的列表在暗网中会是热门商品。
A list of 4,800,000 user accounts would be a hot item on the dark net.
如此庞大的列表可以带来可观的比特币收益,但黑客根本没有出售这些数据的打算。
A list this large could bring in some decent Bitcoin, but the hacker had no intention on selling the data.
黑客再次查看数据库,发现另一个有趣的表,名为member。
The hacker took another look at the database and found another interesting table called member.
它包含了孩子的姓名、生日、性别以及他们父母的ID。
It contained children's names, birthdays, gender, and their parents' ID.
黑客意识到,通过将这两个表结合起来,他可以准确地确定孩子的姓氏和他们的居住地址。
Hacker realized by combining the two tables, he could positively identify what the last name of the child was and where they live.
这个表包含了20万名儿童的信息。
This table contained the information of 200,000 children.
通过查看出生日期,孩子们的平均年龄为五岁。
By looking at the birth dates, the average age of the child was five years old.
黑客关掉电脑,出去散步,思考该怎么做。
Hacker turned his computer off and took a walk to think about what to do.
他感到的愤怒远多于兴奋。
He was much more angry than he was excited.
他愤怒的是,VTech对网站安全如此疏忽,以至于如此多儿童的个人信息如此轻易地被获取。
He was angry that VTech was so careless with securing their site and with the personal information of so many children so easily obtained.
黑客清楚地意识到,他必须让VTech承认他们存在安全问题并加以修复。
It became clear to the hacker he had to get VTech to admit that they have a security problem and to fix it.
对于如此松懈的儿童个人信息安全措施,黑客无法接受,于是开始思考如何解决这个问题。
Having such lax security for personal children data was unacceptable to the hacker, so he began thinking of ways to fix the problem.
他可以自己进去修复,但这无法让VTech学会如何在未来保障安全。
He could go in and fix it himself, but that wouldn't teach VTech how to keep it secure in the future.
他考虑过联系VTech,但觉得他们根本不会听他的,或者即使修复了问题也会否认曾经存在漏洞。
He thought about reaching out to VTech, but he thought they'd never listen to him, or they'd try to fix it and deny it was ever a problem.
黑客花了几天时间思考该怎么做。
The hacker took a few days to think about what to do.
他决定向媒体曝光。
He decided to tell the media.
这样,这个故事将在全球范围内爆发,VTech就必须迅速解决问题。
This way, the story will break worldwide, and VTech would have to solve the problem fast.
他决定联系Vice旗下Motherboard的记者洛伦佐·弗朗切斯奇·比奎雷。
He decided to reach out to Lorenzo Franceschi Biquiray, a reporter for Vice's Motherboard.
Motherboard是一个专门报道计算机相关新闻的媒体,而洛伦佐已经揭露了许多关于数据泄露的精彩报道。
Motherboard is a news outlet specifically covering stories related to computers, and Lorenzo had been breaking a lot of really great stories about breaches.
许多安全记者为人们提供了多种匿名联系的方式,有时通过Signal、PGP加密邮件、加密聊天或其他手段。
Many security reporters provide numerous ways for people to reach them anonymously, sometimes through signal or using PGP emails, encrypted chat, or other means.
黑客通过安全渠道与洛伦佐取得联系,并要求保持匿名。
The hacker connected with Lorenzo securely and asked to remain anonymous.
他将480万条用户记录和20万条儿童记录交给了洛伦佐,并请他曝光这个故事。
He gave Lorenzo the 4,800,000 user records and the 200,000 children records and asked him to break the story.
他明确告诉洛伦佐,自己是一名道德黑客,无意将这些数据用于任何恶意目的。
He clearly told Lorenzo that he was an ethical hacker and had no intention in using this data for anything malicious.
一名黑客对洛伦佐说:'从数据库泄露中获利不是我的做法,尤其是当涉及儿童时。'
A hacker told Lorenzo, quote, profiting from database dumps is not something I do, especially not if children are involved.
我只是希望问题被曝光并得到解决。
I just want issues made aware and fixed.
数据导出非常容易,所以有不良动机的人也能轻易获取。
It was pretty easy to dump, so someone with darker motives could easily get it.
老实说,我能拿到这么多信息,这让我感到恶心。
Frankly, it makes me sick that I was able to get all this stuff.
VTech应该被严惩不贷。
VTech should have the book thrown at him.
他们的安全措施太差了。'
They have shitty security, end quote.
洛伦佐现在必须决定该如何行动。
Lorenzo now had the burden to figure out what to do.
他首先尝试确认黑客是否在说真话,以及这些数据是否是新的且真实的。
The first thing he tried to do is determine if the hacker is telling the truth and if this data is new and legit.
记者最糟糕的做法就是无端指控他人有不当行为。
The worst thing a reporter can do is falsely accuse someone of wrongdoing.
那将是诽谤。
That would be slander.
这会毁掉记者的声誉。
That would ruin the reporter's reputation.
于是洛伦佐将数据包发送给特洛伊·亨特进行验证。
So Lorenzo sent the dump to Troy Hunt to validate it.
特洛伊是一名安全研究员,最著名的是运营网站haveibeenpwned.com。
Troy is a security researcher, most famously known for running the website haveibenponed.com.
特洛伊尽可能收集各种电子邮件泄露数据。
Troy obtains as many email dumps as he can.
这些是出现在安全漏洞中的大型电子邮件地址列表。
These are giant lists of email addresses that are seen in security breaches.
然后,他将这个列表转化为一项公共服务,允许任何人通过他的网站查询自己的邮箱是否曾卷入过泄露事件。
He then turns his list into a public service to allow anyone to search his website to see if their email address was part of a breach.
起初,你可能会认为这样的网站是钓鱼骗局,确实有些是。
At first, you may think a site like that is a phishing scam, and some are.
但特洛伊已经证明自己是正直且可靠的。
But Troy has proven himself to be ethical and legit.
他和他的网站都是值得信赖的。
He and his website are trustworthy.
他的数据库中包含了超过40亿个电子邮件地址,这些数据均来自所有公开的泄露事件。
He has over 4,000,000,000 email addresses in his database, which he gathered from all public breaches.
特洛伊查看了洛伦佐提供的这份新数据集。
Troy took a look at this new dump from Lorenzo.
他发现数据库中的密码字段并未如声称的那样被加密。
He found the password field wasn't encrypted in the database like it said it was.
相反,密码是以一种基础的、未加盐的MD5哈希方式存储的。
Instead, the passwords were stored using a basic, unsalted m d five hash.
无需深入解释MD5是什么,只需知道以这种方式存储密码是极不安全的做法。
Without going into too much detail of what MD5 is, just know it's bad security practice to store your passwords this way.
有些MD5哈希值,你只需在Google上搜索就能找到对应的密码。
Some MD5 hashes, you can simply Google and find the password.
有一些超级计算机可以暴力破解MD5哈希,并且速度相当快。
There are supercomputers that can brute force an MD5 hash and crack it fairly quickly.
将密码以MD5哈希形式存储是严重的安全缺失。
Storing passwords as MD5 hashes is a severe lack of security.
Troy最初对这一点感到震惊。
Troy was at first shocked by this.
随后,他前往该网站查看其实际样子。
He then went to the website to see what it looked like.
他立即注意到该网站 anywhere 都没有使用HTTPS。
He immediately noticed the site doesn't use HTTPS anywhere.
不是用于身份验证或API,什么都没有。
Not for authentication or the API, nothing.
他还注意到该网站运行的是ASP 2.0,而到那时微软已经停止对该版本的支持超过四年了。
He also noticed the site was running ASP two point zero, which by that time had been unsupported by Microsoft for over four years.
你还注意到网站的某些部分泄露了比应有更多的情报,返回了令人惊讶的错误信息。
You also noticed some parts of the website were leaking more information than they should, returning errors with surprising results.
登录失败的消息实际上会显示用于登录的SQL查询。
A failed login message would actually show the SQL query used to log in.
Troy对仅通过使用网站而无需尝试黑客攻击就能收集到的细节感到震惊。
Troy was shocked by the details he could gather simply by using the site and not even trying to hack it.
这份数据转储通过了Troy的初步检验,但由于接近500万条用户记录,他希望有人能帮忙验证内容的真实性。
The dump passed the sniff test for Troy, but at almost 5,000,000 user records, he wanted help to verify the contents were legit.
Troy的网站‘我是否被黑过’取得了巨大成功,他还提供了一项额外服务。
Troy's website, have I been pwned, was wildly successful, and he offered an additional service.
你不仅可以检查自己的邮箱是否曾出现在数据泄露中,还可以将你的邮箱提供给他,以便他在未来任何新的泄露事件中通知你。
Not only could you check your email to see if it had been in a breach, but you can also give him your email and he'll notify you if it shows up in any future breaches.
到那时,特洛伊的这个邮件监控列表已有近30万订阅者。
By this time, Troy had almost 300,000 subscribers to this email watch list.
特洛伊浏览了他的订阅者名单,试图找出那些也出现在VTech用户数据泄露中的用户。
Troy looked through his subscribers and tried to find any that also showed up in the VTech user dump.
他确实找到了许多匹配的电子邮件地址,于是联系了这些人。
He did in fact find many matching email addresses, so he reached out to those people.
他询问他们是否拥有VTech账户,并确认家庭地址和ISP信息是否准确。
He asked if they had a VTech account and asked if the home address and ISP were accurate.
以下是他们的回复。
This is what their responses were.
是的。
Yes.
信息准确。
That's accurate.
我确实注册过VTech,以便为一个玩具笔记本电脑下载附加内容。
I did register at VTech so I could download add ons for a toy laptop.
是的。
Yes.
这是准确的。
That is accurate.
这是一个旧地址。
It's an old address.
我当时确实在那个ISP,所以我可以核实这些信息。
I was at that ISP that that time so I can verify the info.
我当时也会用VTech网站为我女儿下载内容。
I would have used the VTech website for my daughter around that time too.
是的,我在2014年购买了CoraCup后访问过VTech Learning Lodge。
Yes, I did access VTech Learning Lodge in 2014 after purchasing CoraCup for my child.
为了个性化其语音激活功能,你必须注册Learning Lodge。
In order to personalize its voice activated feature, you had to join the Learning Lodge.
此时,Troy确信数据泄露是真实的,并将他的发现告诉了Lorenzo。
At this point, Troy was convinced the dump was legit and told Lorenzo what he found.
本集由Vanta赞助。
This episode is sponsored by Vanta.
客户信任可以成就或摧毁你的业务。
Customer trust can make or break your business.
随着你的业务增长,你的安全和合规工具也会变得越来越复杂。
And the more your business grows, the more complex your security and compliance tools get.
这可能会变成混乱,而混乱并不是一种安全策略。
It can turn into chaos, and chaos isn't a security strategy.
这就是Vanta发挥作用的地方。
That's where Vanta comes in.
把Vanta想象成一位24小时在线的AI驱动安全专家,它能与你一同成长。
Think of Vanta as your always on AI powered security expert who scales with you.
Vanta自动完成合规工作,持续监控你的控制措施,并为你提供合规与风险的单一信息来源。
Vanta automates compliance, continuously monitors your controls, and gives you a single source of truth for compliance and risk.
无论你是像Cursor这样的快速成长型初创公司,还是像Snowflake这样的大型企业,Vanta都能轻松融入你的现有工作流程,让你持续发展一家客户可以信赖的公司。
So whether you're fast growing startup like Cursor or an enterprise like Snowflake, Vanta fits easily into your existing workflows so you can keep growing a company your customers can trust.
请前往 vanta.com/darknet 开始使用。
Get started at vanta.com/darknet.
拼写是 v-a-n-t-a。
That's spelled vanta.
vanta.com/darknet。
Vanta.com/darknet.
到这个时候,洛伦佐已经多次联系过VTech。
By this time, Lorenzo had already reached out to VTech multiple times.
洛伦佐一次次地得不到回应,或者被转接到其他地方。
Over and over, Lorenzo was getting no response or being redirected to somewhere else.
最终,几天后,洛伦佐收到了来自VTech发言人彭Grace的以下回复。
Eventually, days later, Lorenzo got the following response from a VTech spokesperson named Grace Peng.
引述:11月14日,一个未经授权的第三方访问了我们在Learning Lodge应用商店客户数据库中的客户数据。
Quote, on November 14, an unauthorized party accessed VTech customer data on our Learning Lodge App Store customer database.
在您提醒我们之前,我们并未察觉到这次未经授权的访问,结束引述。
We were not aware of this unauthorized access until you alerted us, end quote.
VTech声称他们收到了Lorenzo的邮件,第二天发现了黑客攻击的证据,三天后发布了新闻稿并通过电子邮件通知了客户。
VTech claims they received the email from Lorenzo, found evidence of the hack the next day, then three days later, issued a press release and notified their customers through email.
他们最初的新闻声明对被盗数据和受影响人群的描述含糊不清。
Their initial press statement was vague and unclear as to what was taken and who was impacted.
他们还表示密码已加密,但技术上来说,MD5哈希并不是一种加密方法。
They also said the passwords were encrypted, but technically, m d five hashing is not an encryption method.
时间线也不一致,因为泄露数据的时间戳显示,数据是在他们声称的入侵发生两天后才被获取的。
The date didn't line up either because the data in the dump was time stamped two days after they said the breach took place.
但他们确实关闭了以下网站:planetvtech.com、vsmilelink.com和sleepybearlullabytime.com。
But they did take down the following websites, planetvtech.com, vsmilelink.com, and sleepybearlullabytime.com.
关闭这些网站对VTech来说一定是一个重大的决定。
Taking these websites down must have been a big decision for VTech.
想象一下,你手机上的应用商店超过一个月无法使用。
Imagine the App Store being down on your phone for over a month.
无法更新,无法下载,也无法在设备之间发送消息。
No updates, no downloads, no sending messages between devices.
在那段时间里,他们的玩具失去了主要功能,但公司通过关闭服务器做了正确的事。
Their toys lost major functionality during that time, but the company did the right thing by shutting the servers down.
否则,他们将吸引更多的黑客,面临更大的灾难。
If not, they would have attracted many other hackers and had a much bigger catastrophe on their hands.
一旦这些有漏洞的网站下线并发布了新闻声明,洛伦佐便发表了文章,指出VTech遭遇了数据泄露。
Once the vulnerable websites were offline and a press statement was issued, Lorenzo then published his article indicating VTech suffered a data breach.
他公布了黑客提供给他的所有细节。
He published all the details of what the hacker had given him.
特洛伊·亨特随后发表了一篇严厉的博客文章。
Troy Hunt followed up with a scathing blog post of his own.
VTech安全控制薄弱的消息迅速传播开来。
The news spread quickly of VTech's poor security controls.
世界各地的家长对他们的孩子的信息被泄露感到愤怒。
Parents around the world were outraged their children's information was leaked.
VTech是一家总部位于香港的公司,但在美国、西班牙、英国、德国和法国拥有庞大的市场。
VTech is a company based in Hong Kong, but they have a large market in The US, Spain, UK, Germany, and France.
VTech的股价开始下跌。
VTech's stock began to tumble.
特洛伊也面临着一个道德困境。
Troy was also facing an ethical dilemma.
他的网站haveibeenpwned.com允许用户查询是否自己的邮箱出现在公开的数据泄露中。
His website, haveibeenpwned.com, allowed users to search emails that were seen in public data breaches.
他将480万个电子邮件地址添加到了他的网站上,但拒绝让儿童的名字可被搜索。
He added the 4,800,000 email addresses to his site but refused to make the children's names searchable.
入侵VTech的黑客重新审视了他获取的数据。
The hacker who broke into VTech took another look at the data he grabbed.
令他惊讶的是,他发现实际获取的数据比最初意识到的还要多。
To his surprise, he found even more data than he initially realized.
有一个目录包含了190千兆字节的数据。
There was a certain directory that had a 190 gigabytes of data.
当他浏览时,发现其中包含超过10万张儿童通过平板电脑、手表或笔记本电脑拍摄的照片。
As he looked through it, he found it contained over 100,000 pictures that children took with their tablets, watches, or laptops.
这些照片中许多是重复的、模糊的,或者完全是黑色的。
Many of these photos were duplicates, blurry, or just black.
因此很难估算出实际有多少张照片。
So it was hard to guess as to how many actual photos there were.
黑客进一步查看了他获取的文件。
The hacker looked further through the files he took.
他发现了一些聊天记录,时间跨度长达一年。
He found there were chat logs, which went back a whole year.
这些是孩子平板电脑与父母手机之间发送的所有聊天消息。
These would be all chat messages that were sent between the child's tablet and the parent's phone.
进一步查看数据时,黑客发现了一个包含大量音频文件的目录。
Looking at the data even further, a hacker found a directory full of audio files.
他打开其中一个并播放了它。
He opened one and played it.
他听到的就是这些。
This is what he heard.
我向我精神的旗帜以及那在上帝之下、最优秀的国家所建立的共和国宣誓效忠。
I pledge allegiance to the flag of my spirit and to the republic for which was tense when nation under God and the best of them.
有成千上万这样的录音。
There were thousands of recordings like this.
这些是孩子们对着平板电脑说话的录音。
These are recordings of kids talking into their tablets.
黑客再次联系了洛伦佐,交给他190GB的照片、一整年的聊天记录以及大量语音录音。
The hacker reached back out to Lorenzo and gave him the 190 gigabytes of photos, a year's worth of chat logs, and numerous voice recordings.
几天后,洛伦佐在《Motherboard》上发表了第二篇文章,公布了这些新发现。
A few days later, Lorenzo published a second article on motherboard with these new findings.
我们现在能够看到经过打码的儿童照片,并听到他们的声音。
We are now able to see redacted pictures of children and hear their voices.
这无异于在VTech的伤口上撒盐。
This adds salt to VTech's wounds.
越来越多的家长意识到,他们孩子的个人信息并未得到妥善保护。
More parents are realizing their child's personal information was not kept safe.
一名黑客告诉洛伦佐,他对新闻报道如何传播这一问题的意识感到满意。
A hacker told Lorenzo he was pleased with the way the news stories were spreading awareness of the problem.
他说:‘这正是我所期望的报道量。’
Quote, it is as much coverage as I had hoped for, end quote.
黑客进一步表示,他可能会转向新的目标,‘也许去攻击VTech的竞争对手。’
Hacker went on to say he might move to a new target, quote, maybe into VTech's competitors.
我不确定。
I don't know, end quote.
12月1日,也就是数据泄露两周后,VTech发布了一份常见问题解答。
On December 1, two weeks after the breach, VTech published an FAQ.
其中包含了更多关于此次黑客攻击的信息。
It contained more information about the hack.
VTech声称,被窃取的不仅是20万儿童账户,而是多达630万个儿童账户。
VTech claims that not just 200,000 children accounts were taken, but instead that number was 6,300,000 children accounts.
但VTech并未承认有任何照片被窃取。
But VTech did not admit that any photos were taken.
随后,美国参议员爱德华·马基和乔尔·巴顿致信VTech,指出其行为违反了《儿童在线隐私保护法》(COPPA),该法案于1998年制定,旨在保护儿童在线安全。
Then US senators Edward Markey and Joel Barton sent VTech a letter pointing at the Children's Online Privacy Protection Act, otherwise known as COPPA, an act established in 1998 to protect children online.
他们的信中还提出了九个问题,要求VTech回答,例如:你们收集了哪些关于12岁以下儿童的信息?
Their letter also consisted of nine questions they wanted VTech to answer, such as, what information do you collect on children 12?
你们如何使用这些信息?
What do you use that information for?
你们是否将这些信息出售给他人?
Do you sell any of that to anyone?
你们使用何种加密技术来保护数据?
What encryption is used to secure the data?
VTech并未立即回应,但最终更新了其常见问题解答,以回应其中部分问题。
VTech didn't immediately respond, but they eventually updated their FAQ to answer some of these questions.
在数据泄露一周后,VTech聘请了名为FireEye的安全公司协助应对此次事件。
A week after the breach, VTech hired a security firm called FireEye to help with incident response.
FireEye成功发现了安全漏洞并予以修复。
FireEye was able to find the security issues and resolve them.
1月25日,服务器关闭两个月后,部分恢复了运行。
On January 25, two months after the servers were taken down, they were partially restored.
用户可以再次更新和注册他们的设备,但仍无法使用应用商店。
Users could update and register their devices again, but still could not use the App Store.
breaches一个月后,英国一个专门的犯罪单位在伦敦西部的一个小镇逮捕了一名21岁的男子。
A month after the breach, a specialized crime unit in England caught and arrested a 21 year old man in a town West of London.
他因涉嫌违反1990年《计算机滥用法案》中关于未经授权使用计算机的规定而被逮捕。
He was arrested on a suspicion of unauthorized use of a computer outlined in the Computer Misuse Act of 1990.
该犯罪单位还没收了查获的多件电子设备。
The crime unit also seized multiple electronic items found.
他们还提到,这可能与VTech有关。
They also mentioned this may be related to VTech.
但新闻稿并未公布他们逮捕的男子的姓名。
But the press release did not say the name of the man they arrested.
洛伦佐试图联系这名黑客,但从未得到回复。
Lorenzo attempted to reach out to the hacker, but he never got a response.
在数据泄露两个月后,洛伦佐参加了一个电子产品展览会,发现其中一个展台是VTech的。
Two months after the breach, Lorenzo was attending an electronics trade show and found one of the booths was VTech.
他们正在推出一系列全新产品。
They were launching a brand new line of products.
不过,这些产品并不是给儿童用的。
These weren't for kids, though.
他们出售的是智能灯泡、门传感器和安防摄像头。
They were selling smart light bulbs, door sensors, and security cameras.
当洛伦佐询问VTech市场总监这些产品是否安全时,他回答说:‘我们正在让第三方进行渗透测试,一切都会非常安全。’
When Lorenzo asked VTech marketing director if it's secure, he said they are, quote, going through penetration tests by a third party, and everything is going to be very secure, end quote.
下个月,VTech修改了其网站的服务条款,现在全部用大写字母书写。
The next month, VTech changed the terms of service on their website and now read in all capital letters.
您确认并同意,在您使用本网站期间发送或接收的任何信息可能并不安全,可能被未经授权的第三方截获或获取。
You acknowledge and agree that any information you send or receive during your use of this site may not be secure and may be intercepted or later acquired by unauthorized parties.
看起来,VTech认为只要告知客户他们的数据可能不安全、随时可能被黑客攻击,就能免除自身任何责任。
It appears that VTech thinks they can relieve themselves of any misdoings by simply letting their customers know their data may be insecure and hacked at any time.
几位律师对此发表了评论,认为这样的条款在美国或英国不会被认可,并援引了COPPA法案等规定。
A few lawyers commented on this and believe a clause like that won't hold water in The US or UK, citing things like COPPA laws.
许多政界人士和州检察官联系了VTech,详细讨论COPPA法案。
Numerous politicians and state attorneys contacted VTech to discuss the COPPA laws in detail.
VTech已更新其隐私政策,以更符合COPPA的要求。
VTech has updated their privacy policy to be more compliant with COPPA.
例如,他们现在在隐私政策中声明,所有图片和语音消息在存储时都会被加密。
For instance, they now state in their privacy policy that all pictures and voice messages are encrypted when stored.
在数据泄露之前,BTech的股价就呈下降趋势。
BTech's stock was on a downtrend before the breach.
泄露事件发生后,股价下跌了13%。
And after the breach, the stock dropped by 13%.
三个月内,股价又回升至泄露前的水平。
Within three months, it was back above where it was before the breach.
他们的玩具继续在全球主要玩具商店销售。
Their toys continued to be sold in major toy stores around the world.
在数据泄露后的几周内,几位愤怒的家长起诉了VTech北美公司。
In the following weeks after the breach, several upset parents sued VTech North America.
这些诉讼被合并为一起集体诉讼。
The suits were consolidated into a single class action lawsuit.
原告包括八名成年人和十四名儿童。
Plaintiffs included eight adults and 14 children.
一年半后,即2017年7月,该案提交法官审理。
A year and a half later, in July 2017, the case went before a judge.
VTech请求法官驳回此案,法官予以批准。
VTech asked the judge to dismiss the case, which the judge granted.
法官驳回此案,因为原告无法证明他们受到了实际损害。
He dismissed the case because the plaintiffs could not show how they were harmed.
法官未能找到任何证据表明原告的身份被盗或遭受了其他损害。
The judge could not find any proof that identity theft or any damage was done to the plaintiffs.
法官援引洛伦佐的文章指出,此次泄露是由一名无意恶意使用数据的人所为。
The judge cited Lorenzo's article saying the breach was done by someone who did not have any intention to use the data in a malicious manner.
这个故事有了最新进展。
There's an update to this story.
2018年1月8日,联邦贸易委员会(FTC)认定VTech违反了COPPA法规。
On 01/08/2018, the FTC did find VTech to have violated COPA laws.
VTech同意支付FTC处以的65万美元罚款,但他们也发布了一份新闻稿,声称自己并未违反任何法律。
VTech agreed to pay the $650,000 fine imposed by the FTC, but they also issued a press release saying they haven't violated any laws.
他们还被要求修订其安全计划,并在未来二十年内进行安全审计。
They're also required to revise their security program and conduct security audits for the next twenty years.
我们尚未看到此次数据泄露的内容出现在任何暗网网站上。
We have not seen the contents of this dump show up on any dark net site.
这让我相信,这名黑客遵守了他的承诺,没有试图从他窃取的数据中牟利。
This leads me to believe the hacker upheld his promise and not try to profit from the data he stole.
VTech的常见问题解答中有一个问题,询问被逮捕的黑客后来怎么样了。
The VTech FAQ had a question on it asking what happened to the hacker who was arrested.
一年多来,该常见问题解答只是引导人们查阅逮捕该黑客的执法部门发布的新闻稿。
For over a year, the FAQ simply referred people to the press release put out by the crime unit that arrested him.
这份新闻稿信息极少,甚至没有提及他的姓名。
The press release had very little information and didn't even include his name.
2016年12月,也就是数据泄露发生一年多后,VTech更新了其常见问题解答,对这个问题给出了不同的回答。
In December 2016, over a year after the breach occurred, VTech updated their FAQ with a different answer to this question.
他们称,被捕的男子仅在2016年11月收到了警方的正式警告。
They said the man who was caught simply received a formal police caution in November 2016.
如果这是真的,意味着他在收到警方警告之前被拘留了一整年。
If this is true, it means he was detained for a full year before receiving a police caution.
警方警告通常用于轻微犯罪,有时是为了节省填写完整警方报告的流程,但仍将犯罪记录在案。
Police cautions are usually reserved for minor crimes to sometimes save on filling out full police reports but still put the crime on the record.
也许常见问题解答中的‘ear’是个拼写错误。
Perhaps the FAQ has a typo on the ear.
即使到现在,两年过去了,黑客究竟遭遇了什么仍然不清楚。
Even now, two years later, it's still unclear exactly what happened to the hacker.
我们不知道他是否真的被逮捕了。
We don't know if he was arrested or not.
我们甚至不知道他的名字或他的状况。
We don't even know his name or his status.
如果他真的只收到了警方警告,那么这个故事就结束了,但他可能仍然被关在某个地方的监狱里。
If he did only receive a police caution, then the story's over, but he might still be sitting in jail somewhere.
虽然这名黑客确实犯了罪,但他的意图仅仅是成为一名举报者,主要目标是改善儿童数据的安全性。
While the hacker did commit a crime, his intention was simply to be a whistleblower with his primary goal of improving the security of children's data.
您正在收听《暗网日记》。
You've been listening to Darknet Diaries.
如需节目笔记和链接,请访问 darknetdiaries.com。
For show notes and links, check out darknetdiaries.com.
音乐由 Ian Alex Mack、Kevin McCloud 和 Chris Zabriskie 提供。
Music is provided by Ian Alex Mack, Kevin McCloud, and Chris Zabriskie.
关于 Bayt 播客
Bayt 提供中文+原文双语音频和字幕,帮助你打破语言障碍,轻松听懂全球优质播客。